DNS Firewall Overview
The DNS firewall section allows for the control and flow of traffic through the SSE service DNS firewall.
What is DNS Firewall?
A DNS Firewall provides protection at the Domain Name System (DNS) level by controlling which domain names can be resolved into IP addresses. It blocks access to malicious, suspicious, or unauthorized domains before a user or device can establish a connection. By filtering DNS queries against threat intelligence feeds or custom blocklists, a DNS Firewall can prevent phishing attacks, malware downloads, command-and-control (C&C) communications, and data exfiltration attempts.
Because DNS operates at the very beginning of most internet connections, this layer of defense stops threats early — reducing the risk of infection, improving visibility into network activity, and helping enforce security and compliance policies across users and devices.
DNS Firewall Menu
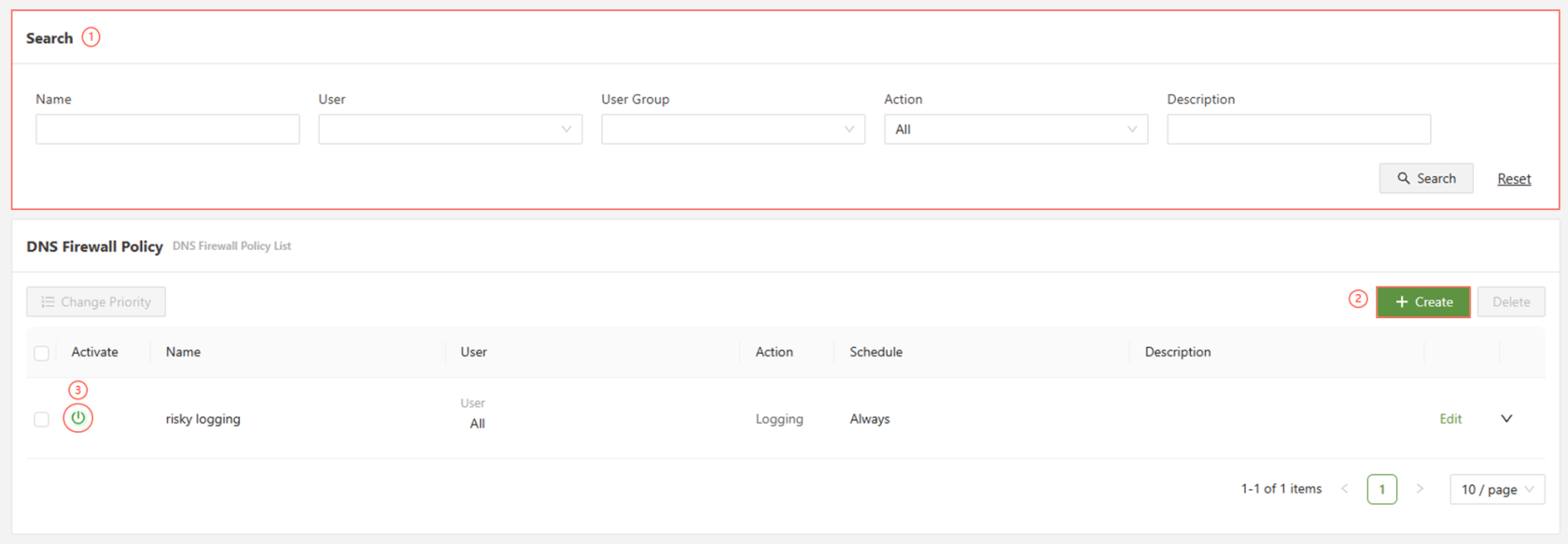
| Search | Allows for the user to search for the policy using a set of parameters |
| Create | Opens up the policy creation menu |
| Activate | Turns on/off a previously created policy |
DNS Firewall Policy Menu
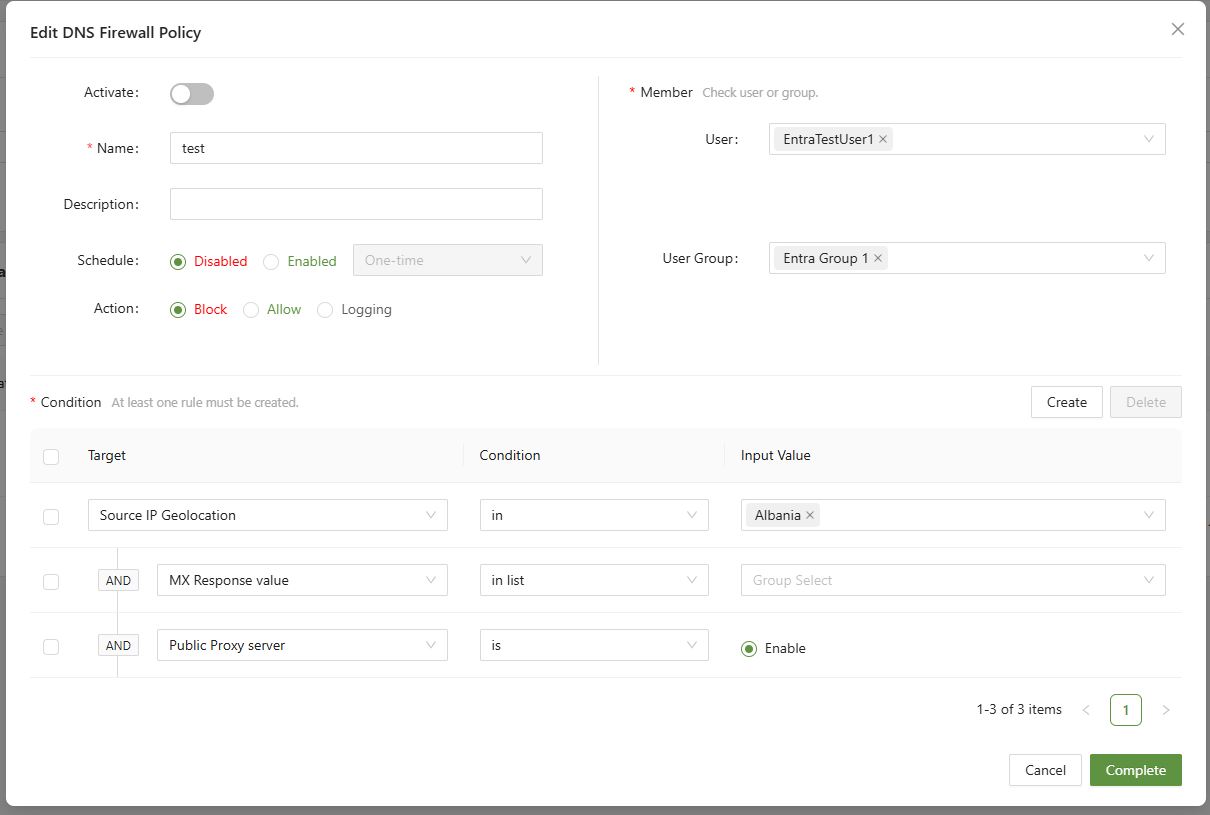
Simple select the users to apply the policies to, and select the target. A list of targets is below:
| Risky Websites | Blocks access to domains classified as malicious, phishing, or associated with malware, based on threat intelligence. Can be configured further in Signature Management |
| Source IP | Applies DNS filtering rules only to requests originating from specified internal IP addresses or IP ranges |
| Source IP Geolocation | Targets DNS traffic coming from devices located in specific countries, useful for applying region-specific rules or restrictions. |
| HTTP Category | Filters domains based on content categories (e.g., gambling, adult, social media), allowing for policy enforcement by site type. Can be configured further in HTTP Category Management |
| FQDN | Matches DNS queries for specific fully qualified domain names, enabling you to block or allow exact domains like example.com. |
| Resolved IP | Targets DNS responses that resolve to specific IPs or ranges, allowing control over where a domain is directing traffic. |
| Resolved IP Geolocation | Filters DNS responses based on the geographic location of the destination server IP, helping restrict access to or from certain regions. |
| CNAME Response Value | Inspects CNAME records in DNS responses and applies policies if the alias points to a flagged or restricted domain. |
| MX Response Value | Applies filtering based on Mail Exchange (MX) records to control domains involved in sending or receiving emails. |
| PTR Response Value | Filters based on reverse DNS lookups (PTR records), allowing policies based on the resolved domain of an IP address. |
| TXT Response Value | Analyzes TXT records in DNS responses, often used for SPF, DKIM, or verification records, allowing policy based on specific text strings. |
| C&C Server | Blocks communication with known Command & Control (C&C) servers, preventing malware from receiving instructions. |
| Public Proxy Server | Denies access to DNS queries resolving to known public proxy or anonymizer services used to bypass security controls. |